Android malware infiltrates 60 Google Play apps with 100M installs

The malicious malware component is part of a third-party library used by all sixty apps that the developers unknowingly added to their apps.
Some of the impacted apps are:
- L.POINT with L.PAY - 10 million downloads
- Swipe Brick Breaker - 10 million downloads
- Money Manager Expense & Budget - 10 million downloads
- GOM Player - 5 million downloads
- LIVE Score, Real-Time Score - 5 million downloads
- Pikicast - 5 million downloads
- Compass 9: Smart Compass - 1 million downloads
- GOM Audio - Music, Sync lyrics - 1 million downloads
- LOTTE WORLD Magicpass - 1 million downloads
- Bounce Brick Breaker - 1 million downloads
- Infinite Slice - 1 million downloads
- SomNote - Beautiful note app - 1 million downloads
- Korea Subway Info: Metroid - 1 million downloads
According to McAfee's research team, which discovered Goldoson, the malware can collect data on installed apps, WiFi and Bluetooth-connected devices, and the user's GPS locations.
Additionally, it can perform ad fraud by clicking ads in the background without the user's consent.
Stealing data from Android devices
When the user launches an app that contains Goldoson, the library registers the device and receives its configuration from a remote server whose domain is obfuscated.
The configuration contains parameters that set which data-stealing and ad-clicking functions Goldoson should run on the infected device and how often.
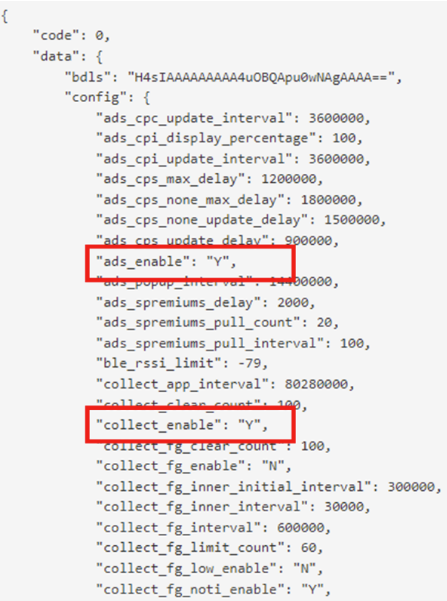
The data collection function is typically set to activate every two days, sending to the C2 server a list of installed apps, geographical location history, MAC address of devices connected over Bluetooth and WiFi, and more.

The level of data collection depends on the permissions granted to the infected app during its installation and the Android version. Android 11 and above are better protected against arbitrary data collection; however, McAfee found that even in recent versions of the OS, Goldoson had enough permissions to gather sensitive data in 10% of the apps.
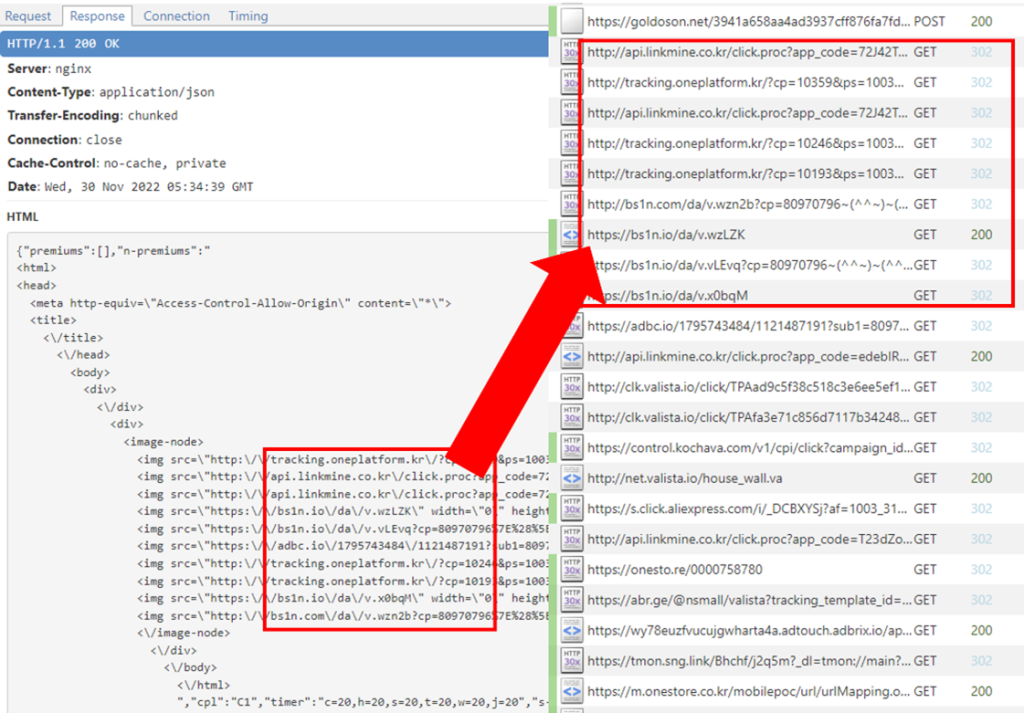
The ad-clicking function takes place by loading HTML code and injecting it into a customized, hidden WebView, and then using that to perform multiple URL visits, generating ad revenue.
The victim does not see any indication of this activity on their device.
Library removed, but risk still there
McAfee is a Google App Defense Alliance member that helps keep Google Play clean from malware/adware threats. As such, the researchers informed Google about its findings, and the developers of the impacted apps were alerted accordingly.
Many of the affected apps were cleaned by their developers, who removed the offending library, and those that didn't respond in time had their apps removed from Google Play for non-compliance with the store's policies.
Google confirmed the action to BleepingComputer, stating that the apps violated Google Play policies.
"The safety of users and developers are at the core of Google Play. When we find apps that violate our policies, we take appropriate action," Google told BleepingComputer.
"We have notified the developers that their apps are in violation of Google Play policies and fixes are needed to come into compliance."
Users who installed an impacted app from Google Play can remediate the risk by applying the latest available update.
However, Goldoson exists on third-party Android app stores too, and the chances of those still harboring the malicious library are high.
Common signs of adware and malware infection include device heating up, battery draining quickly, and unusually high internet data usage even when the device is not in use.

Comments