New RAMBO attack steals data using RAM in air-gapped computers
A novel side-channel attack dubbed "RAMBO" (Radiation of Air-gapped Memory Bus for Offense) generates electromagnetic radiation from a device's RAM to send data from air-gapped computers.
Air-gapped systems, typically used in mission-critical environments with exceptionally high-security requirements, such as governments, weapon systems, and nuclear power stations, are isolated from the public internet and other networks to prevent malware infections and data theft.
Although these systems are not connected to a broader network, they can still be infected by rogue employees introducing malware through physical media (USB drives) or sophisticated supply chain attacks carried out by state actors.
The malware can operate stealthily to modulate the air-gapped system's RAM components in a way that allows the transfer of secrets from the computer to a recipient nearby.
The latest method that falls into this category of attacks comes from Israeli university researchers led by Mordechai Guri, an experienced expert in covert attack channels who previously developed methods to leak data using network card LEDs, USB drive RF signals, SATA cables, and power supplies.
How the RAMBO attack works
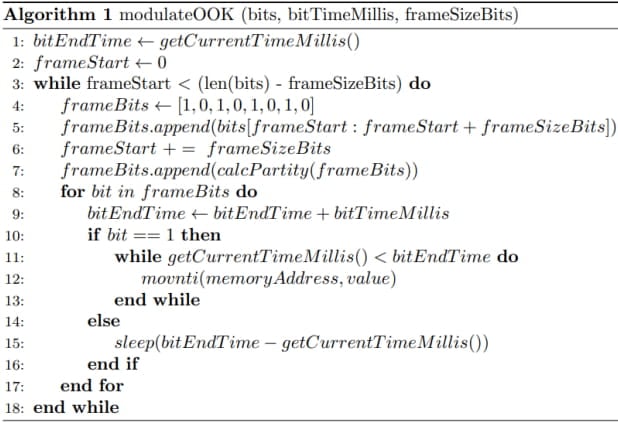
These emissions are essentially a byproduct of the malware rapidly switching electric signals (On-Off Keying "OOK") within the RAM, a process that isn't actively monitored by security products and cannot be flagged or stopped.
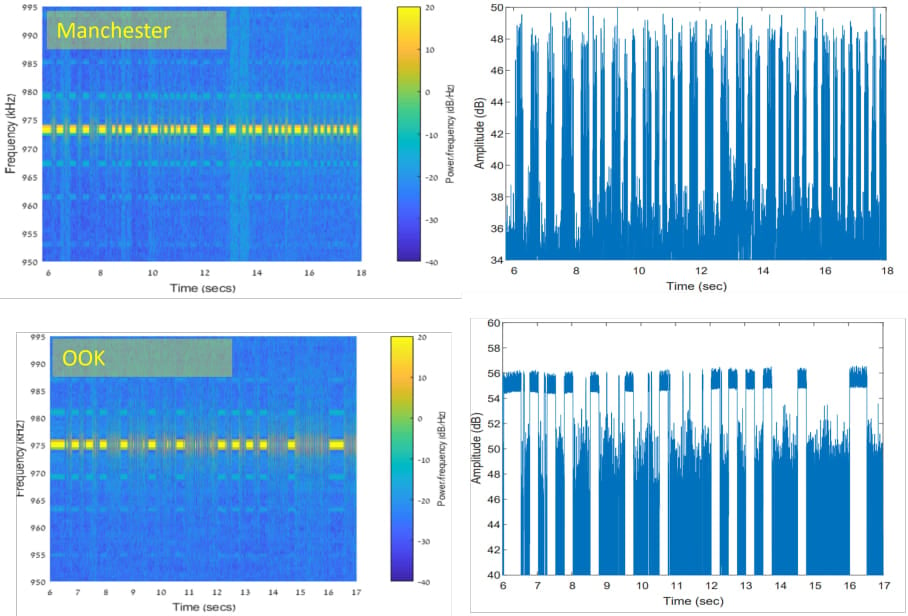
The emitted data is encoded into "1" and "0," represented in the radio signals as "on" and "off." The researchers opted for using Manchester code to enhance error detection and ensure signal synchronization, reducing the chances for incorrect interpretations at the receiver's end.
The attacker may use a relatively inexpensive Software-Defined Radio (SDR) with an antenna to intercept the modulated electromagnetic emissions and convert them back into binary information.
Performance and limitations
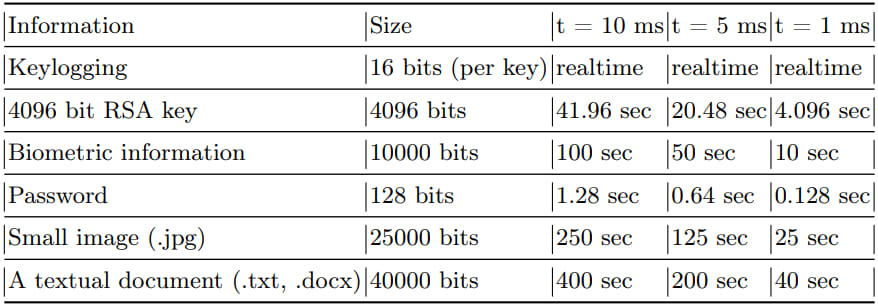
The RAMBO attack achieves data transfer rates of up to 1,000 bits per second (bps), equating to 128 bytes per second, or 0.125 KB/s.
At this rate, it would take around 2.2 hours to exfiltrate 1 megabyte of data, so RAMBO is more suitable for stealing small amounts of data like text, keystrokes, and small files.
The researchers found that keylogging can be performed in real-time when testing the attack. However, stealing a password takes 0.1 to 1.28 seconds, a 4096-bit RSA key takes between 4 and 42 seconds, and a small image between 25 to 250 seconds, depending on the speed of the transmission.
Fast transmissions are limited to a maximum range of 300 cm (10 ft), with the bit error rate being 2-4%. Medium-speed transmissions increase the distance to 450 cm (15 ft) for the same error rate. Finally, slow transmissions with nearly zero error rates can work reliably over distances of up to 7 meters (23 ft).
The researchers also experimented with transmissions up to 10,000 bps but found that anything surpassing 5,000 bps results in a very low signal-to-noise ratio for effective data transmission.
Stopping RAMBO
The technical paper published on Arxiv provides several mitigation recommendations to mitigate the RAMBO attack and similar electromagnetic-based covert channel attacks, but they all introduce various overheads.
Recommendations include strict zone restrictions to enhance physical defense, RAM jamming to disrupt covert channels at the source, external EM jamming to disrupt radio signals, and Faraday enclosures to block air-gapped systems from emanating EM radiation externally.
The researchers tested RAMBO against sensitive processes running inside virtual machines and found that it remained effective.
However, as the host's memory is prone to various interactions with the host OS and other VMs, the attacks will likely be disrupted quickly.


Comments