New Brokewell malware takes over Android devices, steals data
Security researchers have discovered a new Android banking trojan they named Brokewell that can capture every event on the device, from touches and information displayed to text input and the applications the user launches.
The malware is delivered through a fake Google Chrome update that is shown while using the web browser. Brokewell is under active development and features a mix of extensive device takeover and remote control capabilities.
Brokewell details
Researchers at fraud risk company ThreatFabric found Brokewell after investigating a fake Chrome update page that dropped a payload, a common method for tricking unsuspecting users into installing malware.
Looking at past campaigns, the researchers found that Brokewell had been used before to target "buy now, pay later" financial services (e.g. Klarna) and masquarading as an Austrian digital authentication application called ID Austria.
Brokewell's main capabilities are to steal data and offer remote control to attackers.
Data stealing:
- Mimics the login screens of targeted applications to steal credentials (overlay attacks).
- Uses its own WebView to intercept and extract cookies after a user logs into a legitimate site.
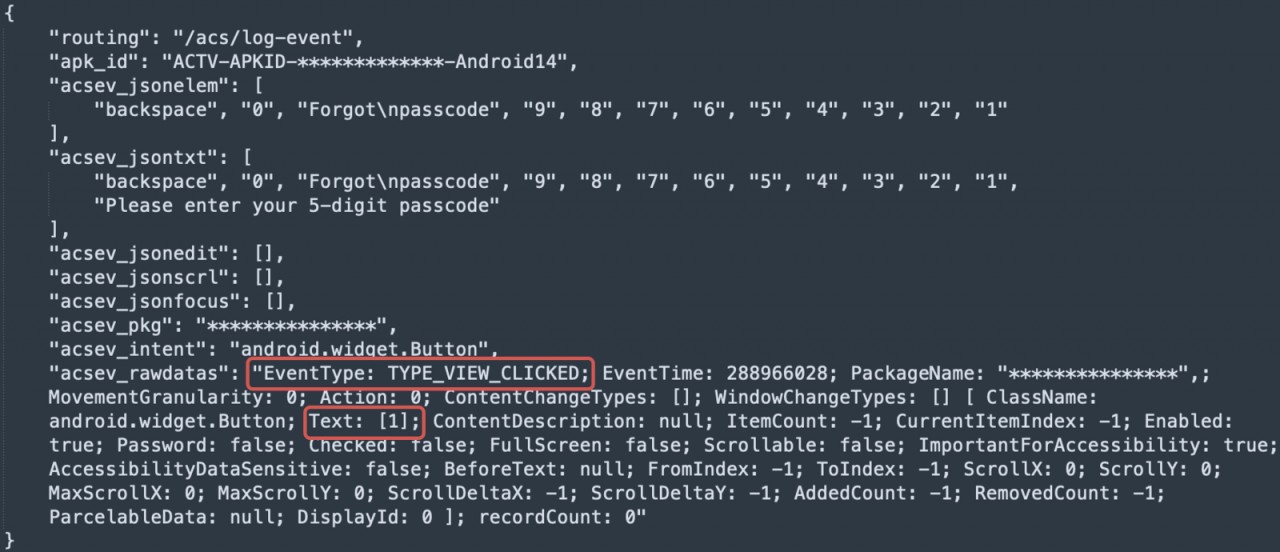
- Captures the victim's interaction with the device, including taps, swipes, and text inputs, to steal sensitive data displayed or entered on the device.
- Gathers hardware and software details about the device.
- Retrieves the call logs.
- Determines the physical location of the device.
- Captures audio using the device's microphone.
Device takeover:
- Allows the attacker to see the device's screen in real-time (screen streaming).
- Executes touch and swipe gestures remotely on the infected device.
- Allows remote clicking on specified screen elements or coordinates.
- Enables remote scrolling within elements and typing text into specified fields.
- Simulates physical button presses like Back, Home, and Recents.
- Activates the device's screen remotely to make any info available for capture.
- Adjusts settings like brightness and volume all the way down to zero.
New threat actor and loader
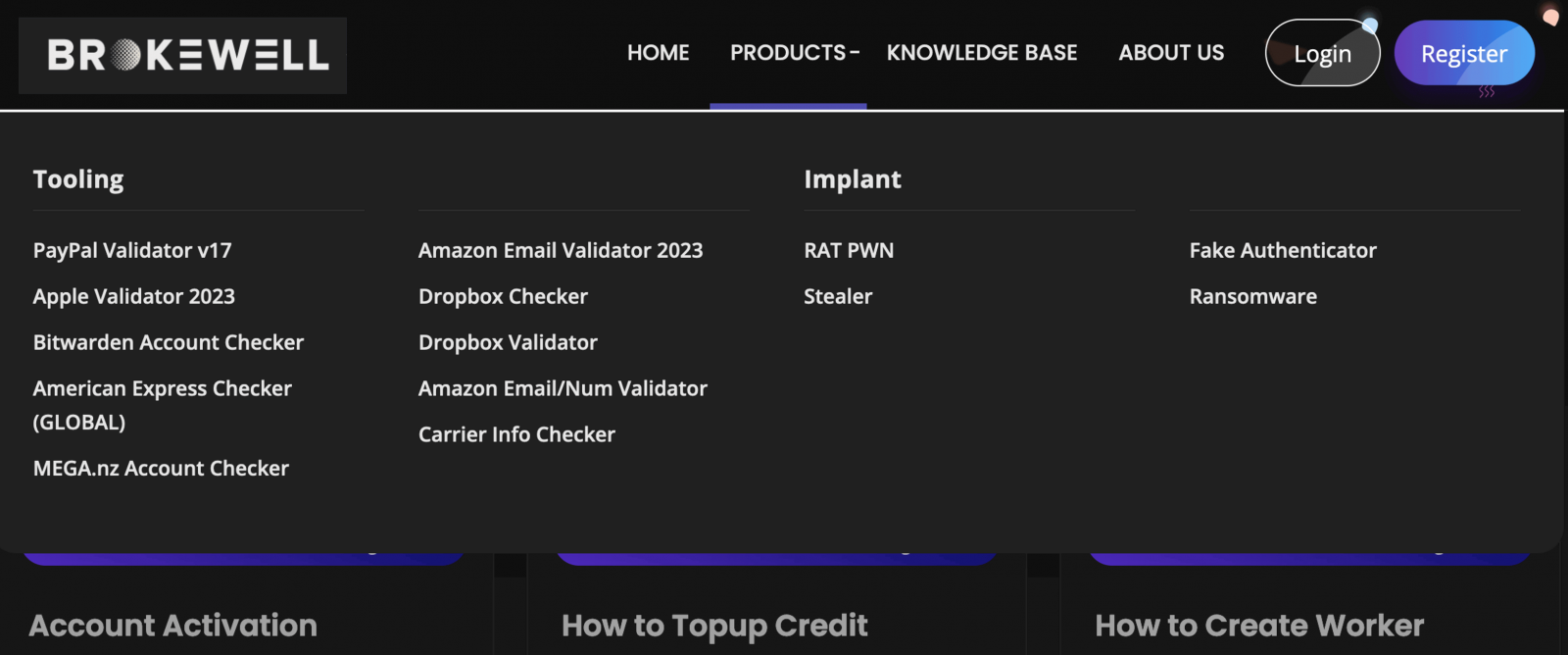
ThreatFabric reports that the developer behind Brokewell is an individual calling themselves Baron Samedit, who for at least two years had been selling tools for checking stolen accounts.
The researchers discovered another tool called "Brokewell Android Loader," also developed by Samedit. The tool was hosted on one of the servers acting as command and control server for Brokewell and it is used by multiple cybercriminals.
Interestingly, this loader can bypass the restrictions Google introduced in Android 13 and later to prevent abuse of Accessibility Service for side-loaded apps (APKs).
This bypass has been an issue since mid-2022 and became a bigger problem in late 2023 with the availability of dropper-as-a-service (DaaS) operations offering it as part of their service, as well as malware incorporating the techniques into their custom loaders.
As highlighted with Brokewell, loaders that bypass restrictions to prevent granting Accessibility Service access to APKs downloaded from shady sources have now become common and widely deployed in the wild.
Security researchers warn that device takeover capabilities such as those avaialble in the Brokewell banker for Android are in high demand among cybercriminals because it allows them to perform the fraud from the victim's device, thus evading fraud evaluation and detection tools.
They expect Brokewell to be further developed and offered to other cybercriminals on underground forums as part of a malware-as-a-service (MaaS) operation.
To protect yourself from Android malware infections, avoid downloading apps or app updates from outside Google Play and ensure that Play Protect is active on your device at all times.
Google has confirmed that Google Play Protect automatically protects users against known versions of this malware.



Comments